Since March 2018, there has been an IATA requirement for all travel agents to be PCI DSS (Payment Card Industry Data Security Standard) compliant. PCI compliance exists to keep your customers data safe. Holiday goers trust you to process their payments in an environment that’s operating adequate security measures, the onus is on you to not let them down.
This includes Retail Travel Agents, Business Travel Agents, Online Travel Agents and Telephone Travel Agents. Every business, no matter how big or small, has to be PCI compliant if they’re handling payment card transactions. Essentially, PCI compliance boils down to taking adequate security measures to protect your customers payment card information. It’s no longer ‘if’ you will be hacked, but ‘when’.
It’s not uncommon for people to think that hackers only target financial institutions, but the truth is every business that handles data is a potential target. This includes the travel sector. A number of travel agents worldwide have been stung by data breaches, the Association of British Travel Agents, Omni Hotels & Resorts, JTB Corp and Essential Travel to name a few. A quick Google search will reveal how prevalent the threat is to travel companies.
![]()
Using Essential Travel as an example, a weakness in their website led to 1.6 million credit card details being stolen. 430,599 of these stolen credentials were thought to have been active, with 733,397 identified as expired. As a result of the exposed data, they were fined £150,000 ($255,000).
According to a study carried out by SPA Future thinking on behalf of the Information Commissioners Office, the fines have had a positive impact on the way organisations handle compliance. The report states that:
- Organisations took their data protection obligations seriously, with revised practices and increased staff training.
- Data protection was given a higher profile, with greater senior management buy-in.
- Staff awareness was raised through targeted campaigns, with the importance of handling data properly made more prominent.
Whilst the fines have overall led to good changes within businesses, these could have been achieved without taking such a heavy financial hit. This is especially true with small businesses, the US’ National Cyber Security Alliance found that 60% of small businesses are unable to sustain their business within six months of a cyber-attack.
Mary Pat Sullivan, analyst for PhocusWright has previously been quoted as saying “The greatest vulnerability for travel agents are those with gross annual sales of $1-10 million.” This is because “agencies with $1-10 million in sales generally have less money to spend on sophisticated, software-based technology tools. Their detection and review are almost entirely manual.”
Unfortunately, there isn’t one ‘thing’ you can do to obtain compliance; some investment of both time and resources is required to achieve and maintain compliance. It doesn’t stop there either, hackers are constantly looking for chinks in your armour and your security team should reflect that. Rather than focussing on compliance itself, you need to focus on keeping customer data sufficiently protected, with the bonus of PCI compliance.
Below are four quick tips to get you on the road to being a PCI compliant travel agency:
Only store card data that’s necessary: According to a report from SecurityMetrics, 61% of merchants store unencrypted card data. If an attacker gains access to your system, they will find unencrypted card data. They know where to look and how to find it. The more unsecure data you store, the more people you have to pay after a data breach.
Keep your systems updated: Web applications, security software and operating systems bring out new versions and patches on a regular basis. These often include fixes for discovered holes in the software such as bugs and security issues. With each new update, often there will be notes detailing what exactly they have changed and why. Whilst this is great for people who want to know what’s new, it also gives hackers the information they need to exploit older versions of the software.
Change your passwords regularly: It’s not uncommon for passwords to be guessed. Hacking tools are available that can and will crack simple passwords. Once cracked, websites are completely vulnerable to whatever the attacker has in mind. It only takes seconds to create a complex password and it can save your business tens of thousands of pounds.
Keep your data backed up: Backups should be automated, systemised and kept offsite. Having an up to date backup could mean the difference between your website being taken down for days, or being back up and running quickly. Reverting to a clean backup is far easier and quicker than going through an entire websites code to find the offender.
Of course however, these measures won’t protect you completely. If you would like to discuss PCI compliance and the services we offer to get you there, please follow the below link for our tailored travel agent PCI services.
But what exactly is required of you as a merchant?
First of all, it’s worth pointing out the 4 levels of merchants as outlined by the PCI standard:
Level 1: Merchants processing more than six million payment card transactions annually via all channels or global merchants identified as level one by any of the card schemes.
Level 2: Merchants processing one million to six million payment card transactions annually via all channels.
Level 3: Merchants processing 20,000 to one million payment card, eCommerce transactions annually.
Level 4: eCommerce merchants only – Merchants processing fewer than 20,000 payment card, eCommerce transactions annually. Non-eCommerce merchants – Merchants processing up to one million payment card transactions annually.
A Guide to PCI DSS Compliance for Travel Agents
The vast majority of travel agents are considered level 4 merchants, so we will focus on level 4 merchants for this blog post. For further information on what’s required of other levels, you can find out more here. So, here’s a brief overview of the steps a level 4 merchant needs to take in order to become PCI compliant:
Step 1:
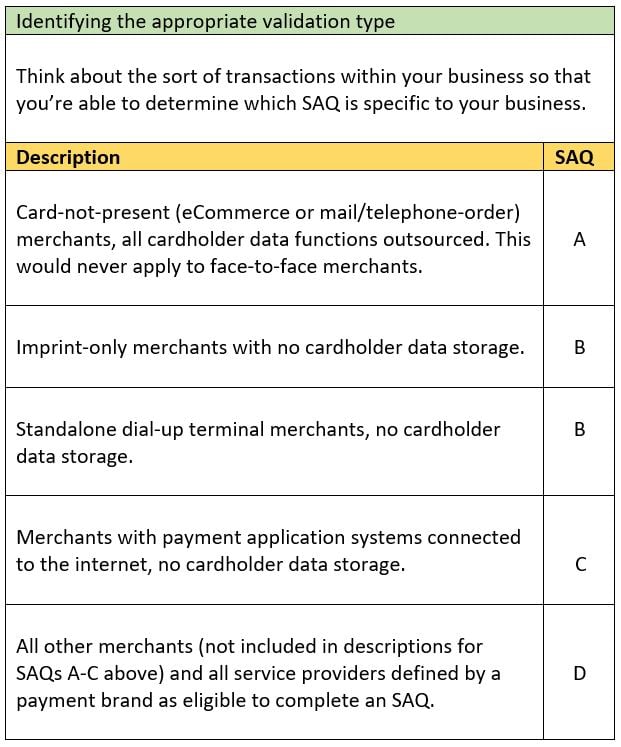
As a level 4 merchant, you will need to complete a Self-Assessment Questionnaire (SAQ). SAQ’s may be shared with an acquiring bank and exist to help organisations with self-evaluating their compliance with PCI DSS. Before jumping in head first, you need to be aware of which SAQ applies to your specific business. Below is a table you can use to identify which SAQ is appropriate for you.
Step 2:
Once you’ve identified which SAQ is relevant for your business, you will need to fill out the required form found here. You will then need to complete the questionnaire according to the instructions outlined in the Self-Assessment Questionnaire Instructions and Guidelines.
If you would like professional assistance in completing the document, you can find a list of the PCI SSC (Payment Card Industry Standards Security Council) verified QSA’s here. Or if you would like a more industry specific helping hand, click the button below for to access our travel agent services.
The PCI SSC also provide a wealth of educational resources to enhance your security awareness within the payment card industry. Such resources can be found here.
Step 3:
If you store customer cardholder data electronically, or if your processing systems are connected to the internet, you will need to organise a vulnerability scan with a PCI SSC Approved Scanning Vendor (ASV). These scans will need to be conducted quarterly. For a list of ASV’s, click here.
Step 4:
Complete the Attestation of Compliance (located within the SAQ).
Step 5:
At this point you should be ready to submit the SAQ, alongside evidence of a passing scan (if this applies to your validation type) and the Attestation of Compliance. This information will need to be sent on to your acquiring bank for review.
PCI DSS doesn’t just apply to the travel industry, it’s a security standard that encompasses any business handling cardholder data. It affects businesses of all sizes, from tiny eCommerce sites to massive international conglomerates; they’re all governed by the same set of security rules. Once you’ve obtained compliance, you’ll have peace of mind that your customers have a satisfactory level of protection from potential fraud. If you're a travel agent trying to obtain compliance, check out our 5 steps to PCI compliance.
The travel agent compliance portal includes self-validation through an easy-to-use, wizard-based PCI self-assessment service. This comes alongside our software solution Serengeti Lite – an end point compliance and cyber health monitoring solution; fully supported by our compliance specialists. It also includes travel-specific policy documentation templates and a guide to demystify the jargon that comes with the standard.
Supported by our team of cyber security specialists, additional options include direct access to one of the world’s leading PCI assessor teams and software to locate unsecured credit card numbers (and other personally identifiable information) to help ensure that they are not left in vulnerable locations and exposed to would be fraudsters.
If you're a travel agent keen on obtaining PCI compliance, you can click here to be taken straight to the sign up page.
Our travel agent tailored compliance services come with:
- An easy-to-use, highly intuitive PCI Self Assessment online portal.
- Full support to simplify and explain cyber security jargon.
- Templated policy documentation to support your compliance.
- Direct access to one of the world's leading PCI Assessor teams.
- Foregenix Cyber Security Technology to simply your compliance and security.
Subscribe to our Blog
TAGS:
Travel Agents Compliance PCI DSS P2PE
Diana Becerra
As an Electrical Engineer & Technology Marketer, I am enthusiastic about promoting new technologies and services that facilitate a connected world, such as cybersecurity, IoT, power systems, energy efficiency and automation. I enjoy merging technical and marketing perspectives to create and implement successful strategies that drive engagement for new products and businesses.
See All Articles