A common piece of advice that floats around online is to never shop on sites without an SSL (Secure Sockets Layer) certification or, more commonly, sites that ‘don’t have the little padlock in the URL’. This is for good reason for, without them, customer data could be stolen within minutes by even the most unskilled of hackers.
But more and more we see websites that, despite requiring no personal data to be shared for use (such as blogs, news, and free video services), still have a certification regardless. Why is this? And how do they secure sites in the first place?
Well to get into that, first, we’ll have to briefly go over Web Protocols, specifically HTTP (which is seen whenever you enter a website into the URL bar).
What are Web Protocols?
Web Protocols are a standard for enabling communication and transfer of information between two places on a network; which is shown through the Open Systems Interconnection (OSI) model. There are 7 layers to this model; Physical, Data Link, Network, Transport, Session, Presentation, Application.
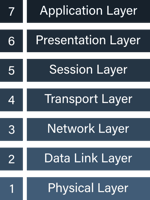 To understand SSL Certificates, we will be focusing on the HTTP protocol on the Application layer.
To understand SSL Certificates, we will be focusing on the HTTP protocol on the Application layer.
What is HTTP?
HTTP, Hypertext Transfer Protocol, is used whenever you wish to see a website. It works as a request-response protocol, meaning that there will be a ‘client’ (your web browser), and a ‘server’ (the website).
The catch is that all information sent through HTTP is written in plaintext, anyone can simply read it, if they are on or have access to the network. The reason for this, and whether or not it is necessary, is widely debated, but the main benefit of this is that troubleshooting is made much simpler, as all the information is simply there for you to look at.
But here the issue arises; man-in-the-middle attacks. More specifically, eavesdropping. Any information sent over the internet is publicly accessible in the moment. Anything you type, click, or interact with is easily-readable for anyone on the network -- intercepting this information as it flows through -- and this doesn’t exactly require much skill or effort to do.
For the aforementioned websites that require no personal information, this isn’t the end of the world, but, for eCommerce sites, this is a very simple but business-destroying oversight.
So how does HTTPS fix this? Encryption.
HTTPS
HTTPS is Secure Hypertext Transfer Protocol. As the name implies, it ensures any information sent through the internet is safe. Of course, it is still interceptable, that cannot be stopped, but it does make it unreadable for anyone trying to nose their way through user activity on websites where it is used.
It does this through encryption, which essentially means it translates plaintext into ciphertext, using a complex algorithm. When encrypting data, both a public key and a private key is generated.
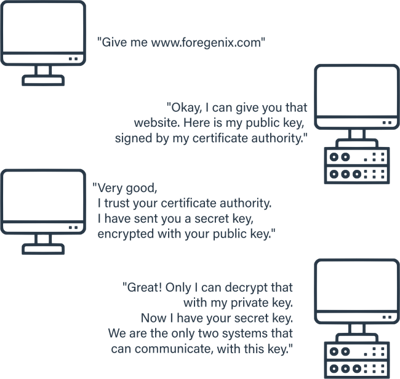
So how does this work? Let’s imagine you’re trying to access Foregenix.com. First of all, you would type, click or paste Foregenix’s URL into your search bar. By doing this, your web browser (the client -- let’s say Firefox) makes a request to Foregenix.
“Give me www.foregenix.com”
Foregenix’s website (the server) would take this request and then create and forward their public key, which has been signed by their Certificate Authority.
The browser would read this and, given that Foregenix is certified by a trustworthy authority, it would create a new secret key, and send it to Foregenix, encrypted by Foregenix’s public key.
Because anything encrypted with their public key can only be decrypted with their private key, the secret key your browser generates and encrypts via their public key will be secure.
With this established, Foregenix and Firefox would agree,
“We are the only two machines that have access to this secret key. It is now safe to send data to each other, which will be encrypted.”
Of course, as I said before, a hacker could still intercept and read these messages as they are being sent. But because they are sent in ciphertext, all they would see is a jumbled, apparently-random, mess of letters, numbers and symbols. This can be brute-forced, but it would take so much time and resources that the large majority of hackers will tell you secured sites are not worth the trouble.
But do I need one?
It wasn’t too long ago that SSL Certifications were only really expected from eCommerce websites, or anywhere that private information is being exchanged. However, as time goes on, it has now become standard for all sites to be secured. One big reason for this is SEO, with Google preferring secured sites over insecure sites, no matter their purpose. Additional to this, the old advice of “Don’t shop on sites without the little padlock” has slowly become “Don’t go to sites without the little padlock.”
Under most circumstances, the answer to the question is a firm ‘yes’. A trustworthy SSL certificate won’t cost you an arm and a leg, and the confidence it gives potential or returning customers (or users) is worth it considering that secure sites are now an expectation.
Is my website safe simply because I have a SSL Certificate?
Short answer? No. You’re in trouble if that is all you have for your website’s security.
As for the long answer: although SSL certification provides one layer of security, your website is not secure. All SSL certificates really do is allow for data sent between a client and server to be encrypted, which only plays a minor role when considering your website’s security.
As an example, if you are using an eCommerce platform, such as Magento, and do not create a custom admin path for your admin panel, an SSL certificate will do nothing to stop hackers from finding this panel and brute-forcing their way in.
Or, if a hacker manages to load malware onto your site which provides a backdoor for later entry, an SSL certificate will not identify and prevent this. It is not a security measure, in this regard.
We advise our customers to scan their websites to identify external vulnerabilities, have a monitoring and alert software to constantly look for internal and external vulnerabilities and a WAF to block 99.9% of online threats.
Our Webscan Solution checks sites for SSL issues. Make sure to get a free scan, if you’re interested. Want to know more? Get in touch at hello@foregenix.com
Subscribe to our Blog
TAGS:
