Where there's a will, there's a way – right?
Absolutely, however, if there is a simpler, better route, why not channel your efforts towards that? Life is complicated enough as it is with constant pressures from all directions and in some cases an ‘easier’ option doesn’t exist, so when a pragmatic approach does, it makes sense to grab it with both hands!
With all the buzz around PCI Point to Point Encryption (PCI P2PE), we have been getting a lot more enquiries around the topic, so have decided to create a couple of blog posts to help clear up some of the basics on PCI P2PE.
Having worked with many of the UK’s mid-large retailers over the years, we’re well aware of the challenges that PCI DSS presents them. Operationally these businesses have their networks and payment systems built for resilience and speed. Security was an after-thought. So when requested to become PCI DSS Compliant within specific timeframes, it is not surprising that many of them have not managed to achieve this. Given the trading environment in recent years, it is not surprising either to see many of the retailers hold off on investing in improving their payment systems – further delaying their PCI DSS Compliance projects.
For some of these businesses, PCI DSS will always seem to be an inconvenient chore, a problem getting in the way of them doing business. Fortunately this mindset is becoming less prevalent as organisations realise that security is the key and that PCI DSS compliance will come naturally to a business that takes their security seriously.
In 2016 we certified the world's first PCI P2PE version 2 application for Optomany and we certify over 40% of the PCI P2PE solutions and over 80% of the PCI P2PE Payment Applications globally.
More recently we certified a P2PE solution for ACS, which subsequently led to the first company in South Africa to reach the requirements for the P2PE standard.
What is P2PE?
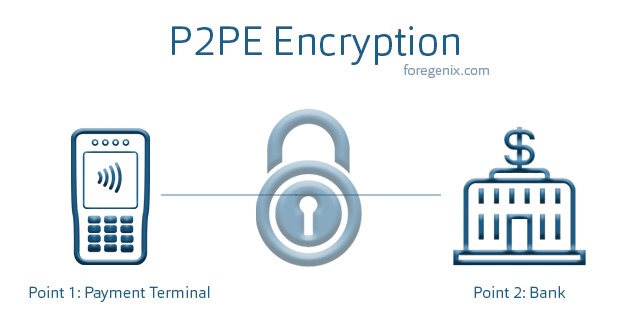
PCI P2PE is the encryption of payment card data from the point of interaction (the chip and PIN device – otherwise known as the PIN Encrypting Device) and then the decryption of the payment card data within a secure environment (generally within the payment processor or acquiring bank) using an approved cryptographic algorithm.
The PCI P2PE is a very detailed standard, requiring a considerable number of controls to be in place to ensure that the resulting solution protects the payment card data appropriately. However, in simple terms, the focus is mainly in the following three areas:
- Managing encryption and decryption devices securely and ensuring chains of custody.
- Manage cryptographic keys securely.
- Building and managing all the applications that run on the devices securely.
If you’re on your P2PE journey and would like to know how we can help you, or simply interested in knowing more about the subject, click the link below for further information.
PCI Scope
Scope is a word that is used often in the PCI world - if you process, store, or transmit card details your business environment is in scope of PCI DSS. The first step in simplifying PCI DSS is to reduce the scope as far as possible and then apply the appropriate controls to the key systems that remain in scope handling the organisation’s transaction data. There is a plethora of risk reduction/scope reducing solutions available. Once the analysis is done on which solutions will address which challenge/control, a number of questions then get asked, such as:
“What is this data worth to me?”
“Why do we need this payment data?”
Often, the answers to the above questions are:
- the payment card data is not worth much to the organisation after processing the transaction; and
- no they do not need the payment data.
So this then leads on to the next questions:
“How can we get rid of this data?”
“How do we make life easier for ourselves?”
Obviously we’re simplifying the discussion, but the point is that if there is an easier way to manage the payment process, which is more secure and means that a retailer can focus on being a retailer, not a technology expert, then surely it would make sense to consider it.
PCI P2PE Validated Solutions
A PCI P2PE validated solution consists of a combination of secure devices, applications and processes that ensure the encryption of cardholder data from the point of interaction (e.g Chip and Pin device) to the solution provider’s decryption environment. By implementing a PCI P2PE solution, organisations are removing the handling of non-encrypted cardholder data from their environment and ensuring security is managed by a validated, specialist, secure third party.
This provides a secure solution for the retail organisation and their customers, as their networks and systems do not handle cardholder data. Consequently, their compliance requirements are significantly reduced.
Foregenix have considerable experience working with PCI P2PE solution providers and merchants who have implemented such solutions into their businesses – we’d be happy to help if you have any questions about how PCI P2PE could help your business.
With all the buzz around PCI Point to Point Encryption (PCI P2PE), we have been getting a lot more enquiries around the topic, so have decided to create a couple of blog posts to help clear up some of the basics on PCI P2PE. This second post provides a high level overview of the domains that make up a PCI P2PE solution.
Any PED used within a P2PE solution must be PTS validated, have SRED enabled and be handled from manufacturer to solution provider to merchant in accordance with the P2PE standard (Domain 1). A full chain of custody should be available to validate this. The solution provider must maintain an inventory of the terminal estate and, at the merchant site, the merchant should handle devices in accordance with the PIM provided by the solution provider (Domain 3).
Note that applications installed on the PED (both those that do and don’t handle cardholder data) must be validated against domain 2 of the standard. Applications and whitelists must be signed by a private key.
All keys injected to the PED must be done within a validated Key Injection Facility (Domain 6: Annex B). Keys can be distributed remotely using asymmetric methods if that mechanism has been validated against Domain 6: Annex A of the P2PE standard.
HSMs used within a decryption environment must be received, stored, deployed and decommissioned in accordance with requirements within Domain 5 of the P2PE standard. HSMs used must be FIPS 140-2 compliant or PCI HSM compliant – what HSMs can be used will also depend on the types of keys used for encryption.
Typical solutions use DUKPT using a BDK installed on the HSM, IPEKs for terminals to create the future keys or unique sets of encryption keys per terminal. These keys are TDES double or triple length. Domain 5 also includes requirements on identification of encryption/decryption failures and authorization failures from specific devices.
All key generation, loading and distribution as well as key component management must be performed in accordance with Domain 6 of the P2PE standard.
Key equivalence must be in place for protecting keys. i.e. any key protecting another key must be of equivalent or greater strength than the key it protects (see ref in image below)
![]()
Validation of all the below requires a lot of policy and procedure documentation as well as evidence of adherence to those policies through logs, shipping bills, minutes of key generation and loading ceremonies, key custodian forms and key component management logs etc.
There is a lot more detail that we can go into, so if you’d like to discuss any particular questions on PCI P2PE, we’d be happy to chat.
PCI Surgery
We offer a free PCI Surgery for organisations looking for extra help with their PCI programs and would be happy to spend time talking through the pros and cons of a PCI P2PE solution too.
You can sign up for the PCI Surgery here – one of our team will be in touch to set up a call with a senior security consultant.
Subscribe to our Blog
TAGS:
Encryption P2PE

