For those unfamiliar with the concept of outsourced payment models, it is essentially the adoption and implementation of eCommerce payment services from commercial Payment Service Providers (PSP) rather than merchants handling the payments themselves. You have probably experienced the concept when you suddenly get whisked off to a different site to present your payment details and then revert back to the eCommerce website once payment has been made. The idea of this being to make sure payment details pass directly from the consumer to the payment service provider who has had their operational security reviewed and certified as PCI DSS compliant.
One way to outsource the payment process is to implement an iFrame. This way when a customer makes a payment the details are sent to the PSP directly and do not sit in the merchants environment. A typical iFrame payment process is shown below.
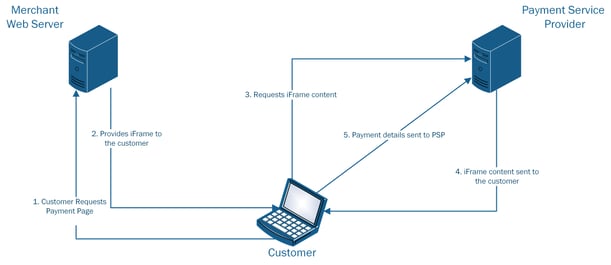
The merchant’s web server provides the iFrame to the client, telling the browser that it should request the content of the iFrame directly from the Payment Service Provider with a unique ID. The iFrame contains the form that asks the customer to enter their payment card details and, on submitting the form, the data is sent directly to the Payment Service Provider, bypassing the merchants web server altogether
The iFrame attack that we have seen recently works as a Man In The Middle (MITM) attack. Instead of the merchants web server telling the client to get the source of the iFrame directly from the PSP, malicious code that is injected in to the website instead requests the iFrame source code from the PSP and then modifies its code, resulting in the client receiving a modified iFrame that submits the data directly to the malicious code on the merchants web server. After the malicious iFrame is submitted by the customer, the malicious code then returns the genuine iFrame, allowing the customer to complete the transaction. Below is an example of the iframe attack:
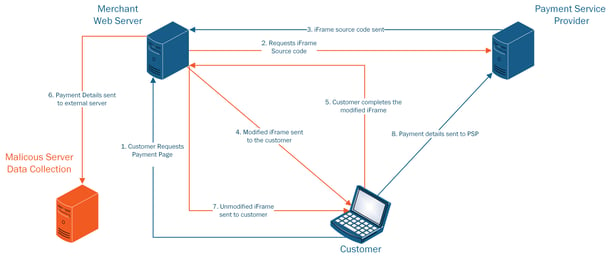
After intercepting the iFrame from the PSP and then manipulating it so that payment card data is submitted back to the merchant’s server instead of the PSP, the malicious iFrame can then be sent to the customer to be completed. Once they complete the form and then press the pay button, the details are sent back to the webserver where the malicious code will write the payment card data to a harvest file located on a third-party server. Alternatively the harvest file may be located on the merchant’s web server to be collected at a later date. Once this step is complete the webserver then packages up the genuine iFrame and serves this to the customer who then completes the form for the second time, which is then sent back onto the PSP.
Either version results in harvested payment card data from the eCommerce website and potentially significant financial penalties for the business.
What can you do?
- Check website source code against known good sources, for example, offline development copies to ensure that you have not been compromised.
- Complete a payment – Why?
- By completing a payment you will be taken through the entire payment process. In completing completing the payment you will be able to tell if your iFrame has been compromised by the amount of times you are asked to enter your payment details. If you have to enter payment details twice then this is a strong indicator that your website has been compromised.
- Card data scanning - If malicious code is harvesting card data to your webserver then card data scanning would be a good step as it will highlight the location of the harvest file.
- Ensure the latest updates are installed on the eCommerce platform.
- Make sure that you change all passwords and review the administrator user accounts in order to ensure that there are no unknown users that have been placed into the database.
- Review firewall rules and block all unnecessary outbound connections. This can limit what an attacker could do once inside your system. In this case it would prevent the attacker from being able to establish an outbound connection to the third party webserver to harvest the card details.
The Proactive Approach
You can very easily protect your online business against these sorts of attacks by implementing a simple four-step defence-in-depth strategy utilising our FGX-Web Protect solution.
We offer a 7 day free trial, which will help you to quickly identify any issues and get your online business protected.
If you need help with understanding the technology or alerts, you have our team on hand to support you and to ensure you have a secure online business.
Subscribe to our Blog

